...
Connect to mayanas instances using SSH to setup IAM Service Principal account. MayaNAS requires a IAM user account with sufficient permissions to manipulate disk attachments for proper sharing and fencing, and also storage read-write access to object storage. It also needs sufficient permission to float the virtual IP across multiple instances. By having separate IAM account for all MayaNAS deployments you can enforce proper security measures as the assigned roles are limited to this project instance only.
Info Please take a note of the AWS_ACCESS_KEY_ID and AWS_SECRET_ACCESS_KEY for the newly created IAM user account.Run aws configure from root shell to provide necessary authentication information. This has to be completed on both the instances for proper High-Availability operation
Code Block language text theme RDark # sudo aws configure AWS Access Key ID [None]: AKIAJ66FNQUXMW6T3YCQ AWS Secret Access Key [None]: I+6DmswWVF5839ylxuyj/+9+76jk3LvdaDIR Default region name [None]: us-west-2 Default output format [None]:Warning Please make sure login to service principal is done as root user.
Secure the SSH to secure the Web console GUI access by changing the default password to something random by running
Code Block language bash # /opt/mayastor/web/genrandpass.sh
Or to set your own password
Code Block language bash # /opt/mayastor/web/changepass.sh Login name (default admin): Login password: Password again:
And then restart the web server for password changes to take effect
No Format # /opt/mayastor/web/stop # /opt/mayastor/web/start
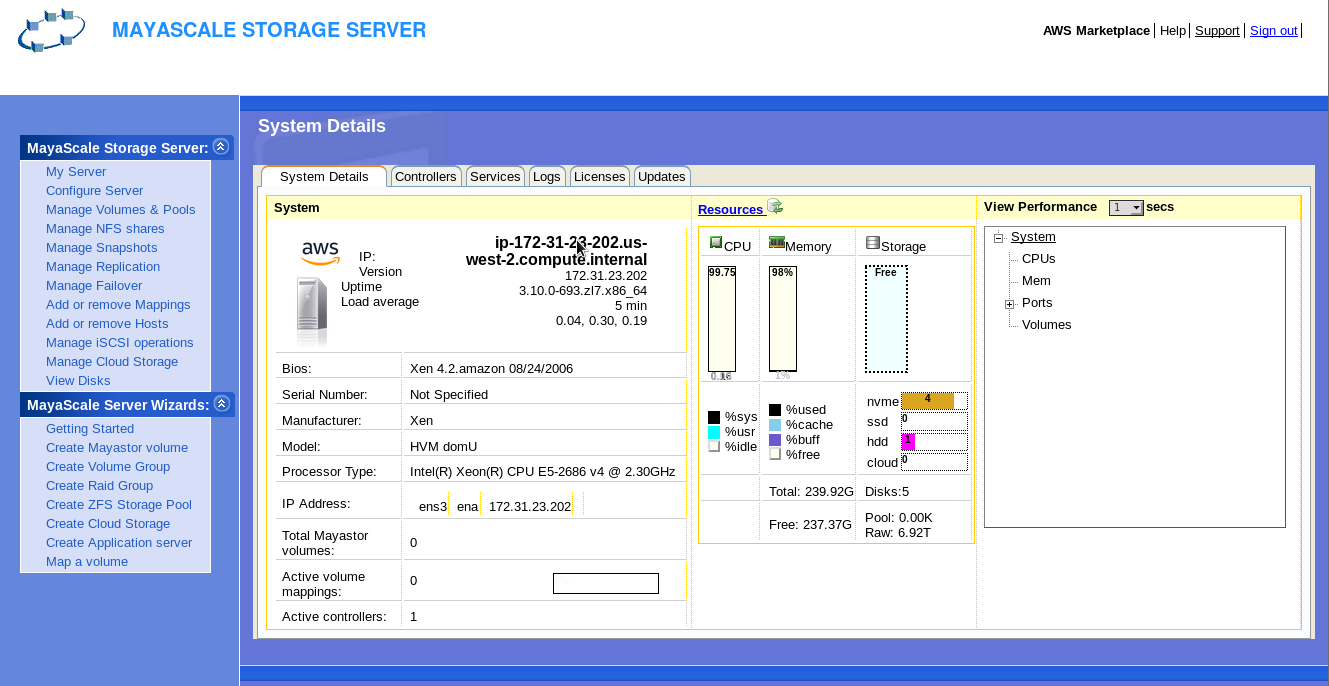
Now you can proceed with High-Availability setup using the wizard from Administration Web console available on http://<mayanas-ip>:2020